LIA Implements Malcat Kesakode for Payload Identification
Malware is constantly evolving in an effort to evade detection and identification, using different kinds of obfuscation and morphing that makes creating a reliable signature more challenging.
To increase the detection capabilities of downloaded payloads, LIA has partnered with Malcat to implement Kesakode in the payload analysis pipeline.
Kesakode - Fuzzy Detections
Compared to static signatures, Kesakode relies a fuzzy hashing to identify malware families. Kesakode extracts artifacts from a sample such as interesting functions, constants and strings. These are used to calculate a fuzzy hash that is queried against the Kesakode database. The result is a similarity score to a known malware families, if known. This helps in identifying known malware families where for example Yara rules have become outdated or does not yet exist.
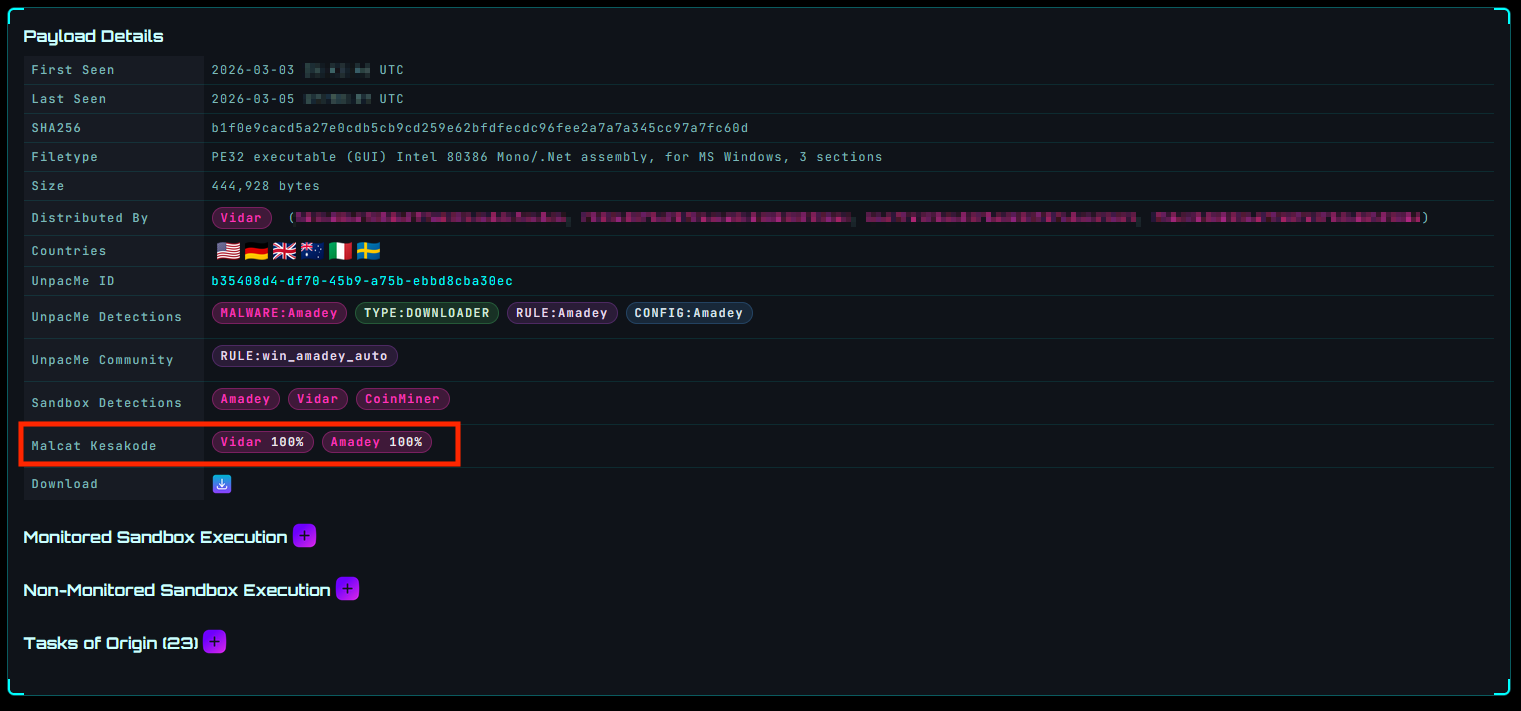
All artifacts from LIA sandbox executions are scanned with Kesakode and the similarity scores are provided in the payload view together with the UnpacMe and sandbox detections as shown in the below figure.
Kesakode detections are searchable in the UI using the kesakode: keyword.
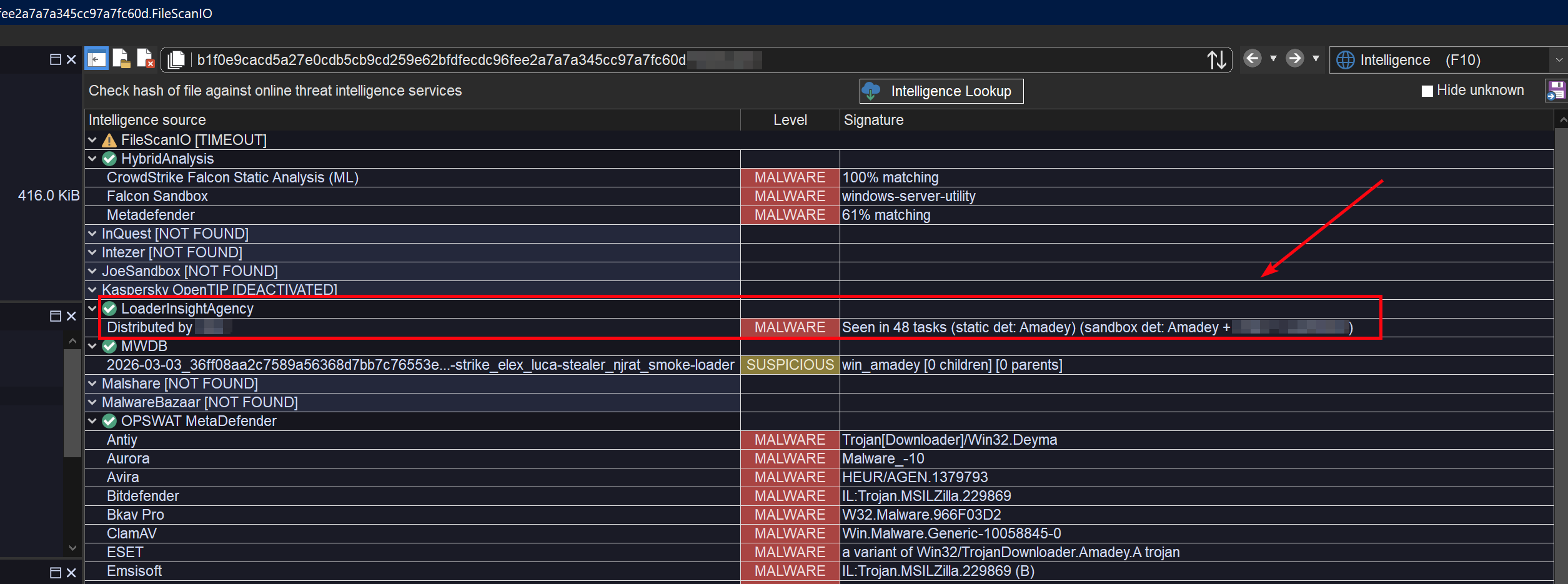
LIA Lookups in Malcat
Malcat is providing a threat intelligence plugin to integrate LIA in the UI, enabling lookup of a SHA256 hash directly in the Malcat UI to get more context about a payload. This includes which family downloaded the payload and any static and/or dynamic detections.
In addition, it is also possible to download a sample from LIA directly from the Malcat UI. Simply grab your API key from the Accounts page and enter it in Malcat.
Read more about Malcat and Kesakode on the official Malcat website.